Ransomware backup architecture fails the moment you design it for accidental failure instead of adversarial intent. Assume the attacker has your runbooks. Not as a theoretical exercise — as an operational reality. Modern ransomware groups conduct reconnaissance that lasts weeks. They map your backup
NTCTech
Ransomware backup architecture fails the moment you design it for accidental failure instead of adversarial intent.
Assume the attacker has your runbooks. Not as a theoretical exercise — as an operational reality.
Modern ransomware groups conduct reconnaissance that lasts weeks. They map your backup infrastructure, recovery dependencies, and retention policies before encrypting a single file.
They are not trying to destroy your data. They are trying to make recovery impossible.
The Thesis
Backup strategies assume failure.
Ransomware assumes recovery.
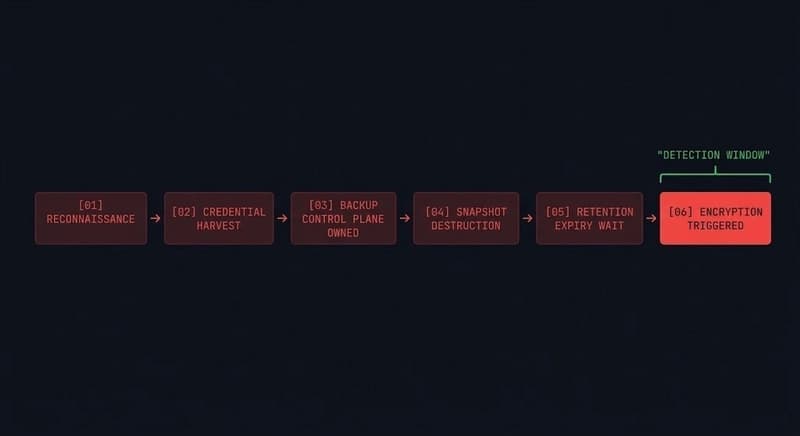
The Six Predictable Attacker Moves
1. Backup Control Plane Compromise
Encryption is not the first move. Owning your backup orchestration system is. Admin credentials, API tokens, altered backup policies — all before you know the attack started.
2. Pre-Encryption Snapshot Destruction
Sophisticated ransomware waits. It maps your snapshot schedules, then destroys recovery points before triggering encryption. Your 30-day retention policy becomes their 31-day patience exercise.
3. The Air Gap Illusion
A true air gap means not reachable via network, identity, or API. The moment your "air-gapped" backup is reachable through anything a compromised account can touch — it is not air-gapped.
4. Runbook Intelligence Leak
Your recovery runbook lives in a wiki that uses the same SSO as your production environment. An attacker with domain access has read your recovery documentation. Your predictable steps become their attack sequence.
5. Immutability Bypass via Management Plane
The storage layer is immutable. The management layer is not. Attackers don't attack the WORM storage — they attack the system that manages the immutability policy.
6. Recovery Path Disruption
Even with intact backups, recovery can be made impossible. Identity unavailable. DNS broken. Orchestration compromised. No clean environment to restore into. Your backups survived. Your ability to use them did not.
The Architectural Fix
- Separate the identity plane of backup infrastructure from production
- Immutable snapshots with retention locks enforced at storage layer, not management layer
- Test air gap reachability actively — if you can reach it from a compromised host, it isn't air-gapped
- Recovery documentation offline and out-of-band
- Management systems that enforce immutability must be as hardened as the storage itself
- Full recovery path drills — not just restore verification, but identity, DNS, and orchestration end-to-end
*Full post with the adversary POV walkthrough, assumptions vs reality block, and complete architectural response at the canonical URL: https://www.rack2cloud.com/ransomware-backup-architecture/
*
Found this useful? Share it!
Read the Full Story
Continue reading on Dev.to
Related Stories
Majority Element
about 2 hours ago
Building a SQL Tokenizer and Formatter From Scratch — Supporting 6 Dialects
about 2 hours ago
Markdown Knowledge Graph for Humans and Agents
about 2 hours ago
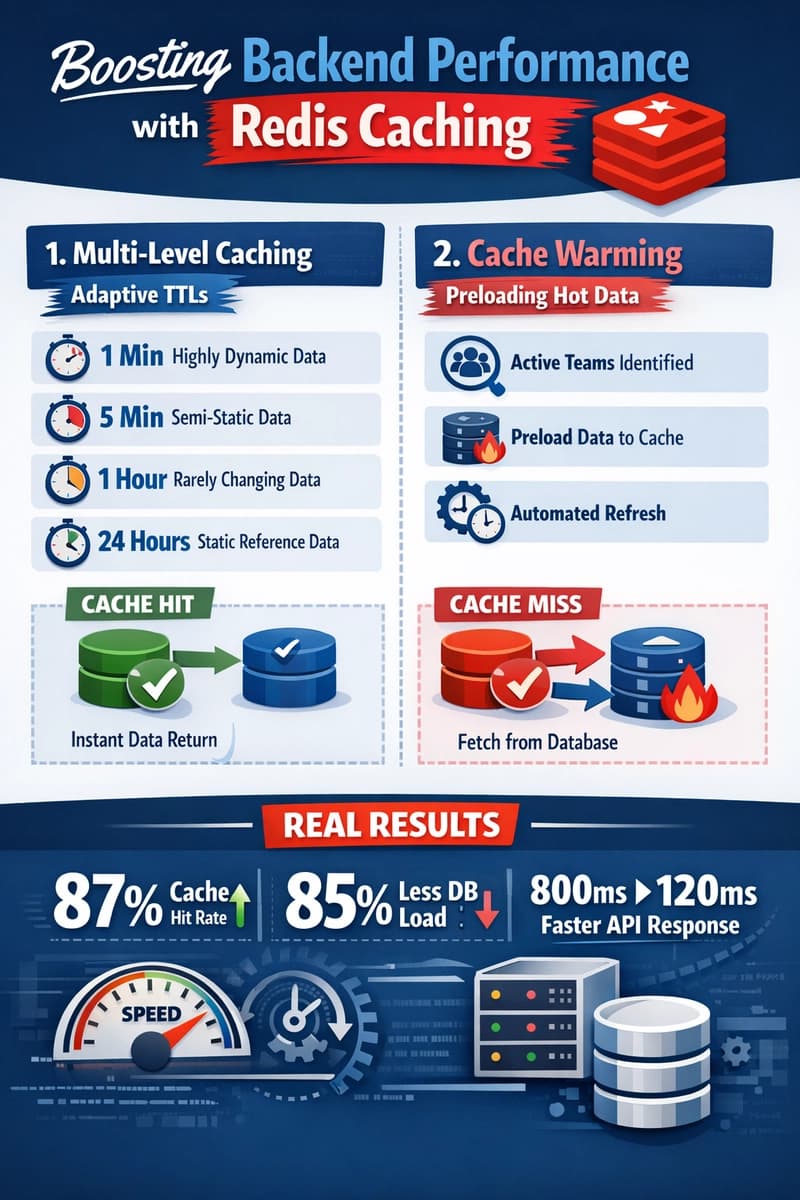
Moving Beyond Disk: How Redis Supercharges Your App Performance
about 2 hours ago