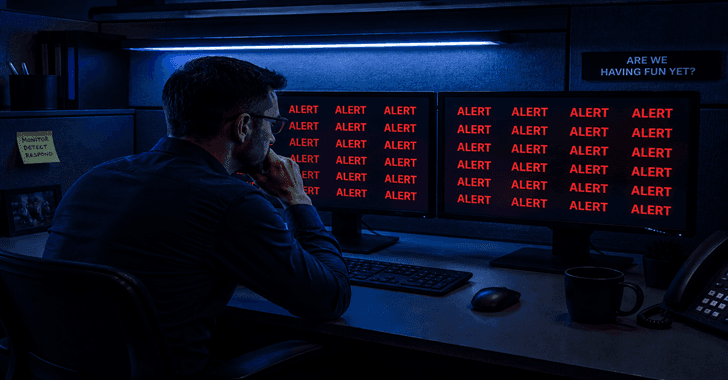
India's Cybersecurity Landscape Clouded by Compelling but Contradictory New Theories
As AI shortens the path from vulnerability disclosure to exploitation, researchers disagree on whether the problem is inadequate security tools or inadequate operational control. The post Two New Reports Offer Competing Explanations for Cybersecurity’s Growing Crisis appeared first on SecurityWeek.