Introduction Advances in AI model-powered exploitation have demonstrated that general-purpose AI models can excel at vulnerability discovery, even without being purpose-built for the task. Eventually, capabilities such as these will be integrated directly into the development cycle, and code will be
Key Insights
10 AI-generated analytical points · Not copied from source
{"$":{"xmlns:author":"http://www.w3.org/2005/Atom"},"name":["Francis deSouza"],"title":["Google Cloud COO and President, Security Products"],"department":[""],"company":[""]}
Original Source
Google Cloud Blog
https://cloud.google.com/blog/topics/threat-intelligence/defending-enterprise-ai-vulnerabilities/Deep Analysis
Original editorial research · AiFeed24 Intelligence Desk
Multi-Source Intelligence
AI-synthesized from 5-10 independent sources
Fact Check
Multi-source verificationFound this useful? Share it!
Read the Full Story
Continue reading on Google Cloud Blog
Related Stories
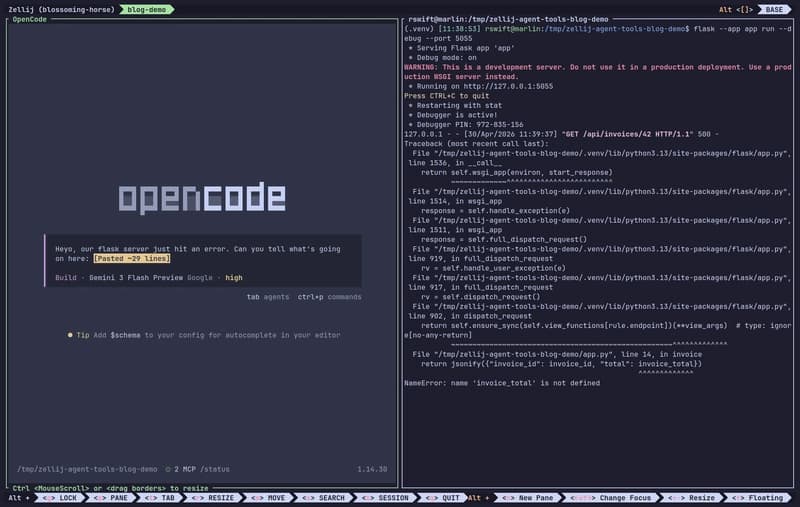
Stop Using Your Clipboard to Share Context
17 minutes ago

NestJS v12 Roadmap: Full ESM Migration, Standard Schema Validation and Modernised Toolchain
about 1 hour ago

Quickbase’s Pave targets vibe coding’s notorious 80% problem
about 2 hours ago

Meta abandons open-source Llama for proprietary Muse Spark
about 2 hours ago
