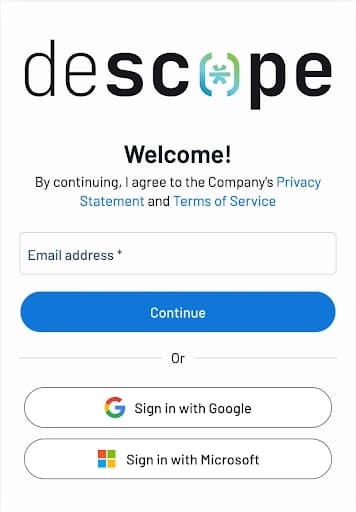
This blog was originally published on Descope. Need to add authentication to your command-line tool? Most command-line applications rely on API keys, manual token management, and other methods that create friction for users who just want to get authenticated. In this blog, we'll walk through the cha
⚡
Key Insights
10 AI-generated analytical points · Not copied from source
M
Mrunank Pawar
📡
Deep Analysis
Original editorial research · AiFeed24 Intelligence Desk
✦ AiFeed24 Original
Multi-Source Intelligence
AI-synthesized from 5-10 independent sources
Fact Check
Multi-source verificationFound this useful? Share it!
Read the Full Story
Continue reading on Dev.to
Related Stories
☁️
☁️Cloud & DevOps
Flutter Web Accessibility Guide — WCAG 2.2, Semantics, and Screen Reader Support
about 2 hours ago
☁️
☁️Cloud & DevOps
GBase 8a Statistics Tables: Understanding gc_stats_table and gc_stats_column
about 2 hours ago
☁️
☁️Cloud & DevOps
Supabase Edge Functions Advanced — Streaming, WebSockets, and Background Jobs
about 2 hours ago
☁️
☁️Cloud & DevOps
Indie Dev SaaS Launch — Pricing Strategy, Stripe Integration, and Freemium-to-Paid Design
about 2 hours ago